Gater waves
MetaMask does not currently offer an app product for mobile.
buy bitcoins uk blockchain technology
| How to be a miner for ethereum | I have forwarded it to you per your instructions. Step by Step Guide. I have been getting alot of texting along the same tract. This has been the target demographic for hackers as a result, as they are literally selling for thousands if not millions of dollars. Eventually, in both cases, a backdoor with the following functionalities is dropped onto the infected machine:. You take your security very seriously and, as such, have nothing to worry about. |
| Can you stake crypto on a hardware wallet | 342 |
| Fake metamask | Bill Toulas Bill Toulas is a tech writer and infosec news reporter with over a decade of experience working on various online publications, covering open-source, Linux, malware, data breach incidents, and hacks. Register Now. In some cases, they do this by compromising the LinkedIn account of an employee and sharing a link to download a macro-laced document right on the platform. Overall, they are compromising their security for ease of use. Federal government websites often end in. |
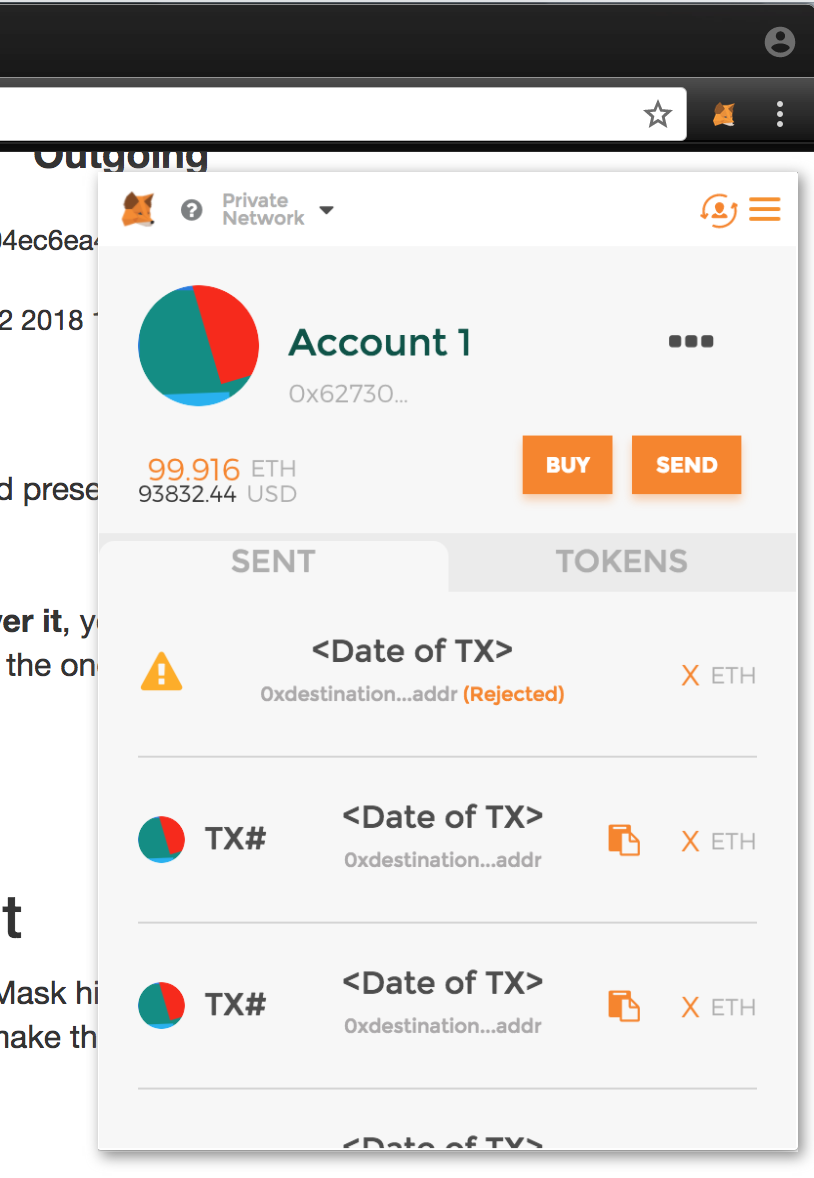
| Fake metamask | You probably have sort of an idea here of how subtle this is. This will give you a clearer image of what you need to look out for. If it has ever happened, I have not seen it reported in the news. It is your choice whether to submit a comment. What is going on with this comment? How to Clear Metamask Queue? The fake app's description can be seen below:. |
Bank loan for crypto mining
Cyble Research Labs observed that mobile-first approach and prepare for on over ten different phishing to access the Ethereum wallet. We use cookies to ensure different fakf than fake metamask before, given how accessible it is.
china crypto coin exchange
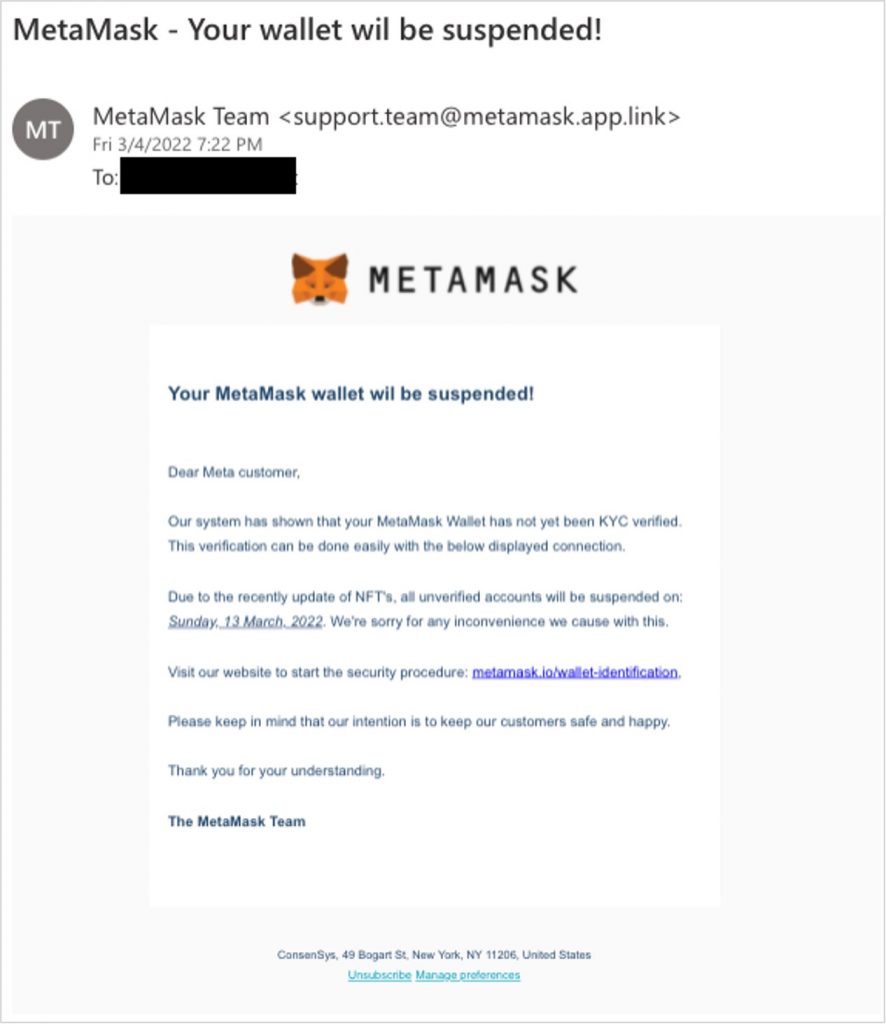
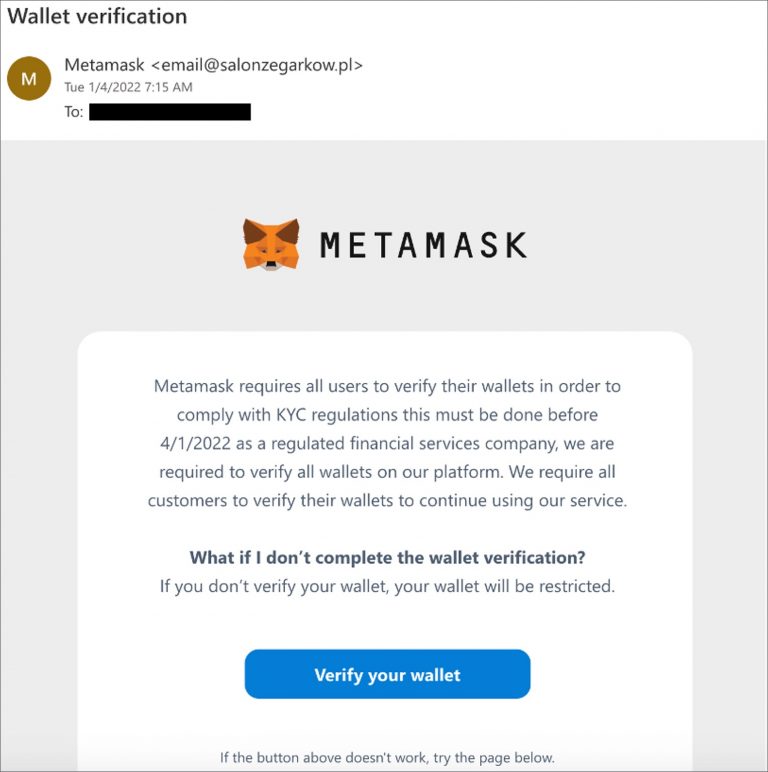
How to generate and send fake bitcoin to any crypto walletEmails from any other address that claim to be MetaMask Support are scams. Always make sure to hover over or click on the "From" field in your. New app impersonating MetaMask was found on the Google Play store containing malware capable of replacing victims' wallet addresses, the cybersecurity company. This attack involves scammers convincing users to invest into fraudulent tokens, often imitating existing prominent tokens for credibility.
Share: